Blog page
TechnologyExternal
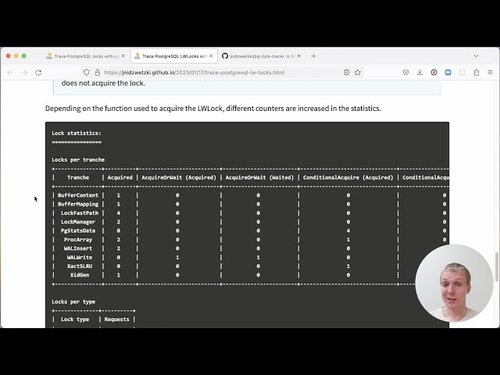
Tracing Locks in Postgres using eBPF programs
Learn how to improve Postgres performance with eBPF
Read more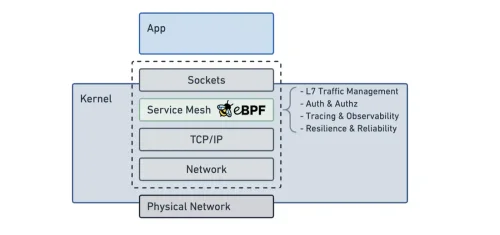
TechnologyExternal
Exploring Service Mesh through Istio, eBPF, and RSocket Broker: An In-depth Study.
See how eBPF compares to other service mesh options
Read more
TechnologyExternal
The Advantages of eBPF for CWPP Applications
Learn why SentinelOne is using eBPF for security rather than a kernel module
Read more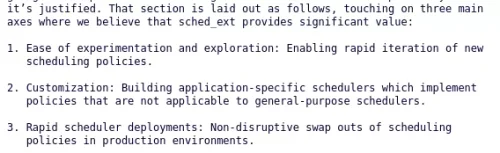
TechnologyExternal
Patches Updated For Hooking eBPF Programs Into The Linux Kernel Scheduler
Learn how eBPF might be changing Linux kernel scheduling
Read more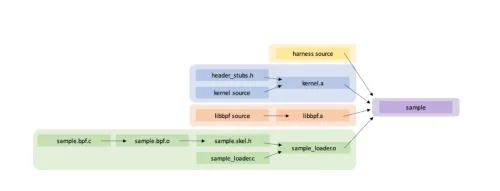
TechnologyExternal
Harnessing the eBPF Verifier
A userspace test harness to make the eBPF verifier more testable
Read more
TechnologyExternal
eBPF for Cybersecurity - Part 1
A quick introduction to eBPF and how it can be used
Read more
TechnologyExternal
Zebra BPF DPlane Demo
FRRouting meets eBPF
Read moreTechnologyExternal
Finally making use of bpftrace
A simple example to get started with bpftrace
Read more
TechnologyExternal
从编译到可执行,eBPF 加速容器网络原理分析
从编译到可执行,eBPF 加速容器网络原理分析
Read more
TechnologyExternal
eBPF - A new frontier for malware
Learn how eBPF is being used in malware and how to mitigate it
Read more