Blog page

Simple Firewall with Rust and Aya
Learn how to use eBPF to create a simple firewall/router
Read more
Zero to Performance Hero: How to Benchmark and Profile Your eBPF Code in Rust
Learn how to create a basic eBPF program in Rust
Read more
A simple pair of eBPF tracepoint handlers
Learn about tracepoint handlers in eBPF
Read more
Ep. #11, Frictionless Observability with Yechezkel Rabinovich of Groundcover
In episode 11 of How It's Tested, Eden Full Goh sits down with Yechezkel Rabinovich of Groundcover to delve into the evolving landscape of observability powered by eBPF
Read more
eBPF Cheat Sheet
A compilation of useful eBPF commands for a DevSecOps workflow
Read more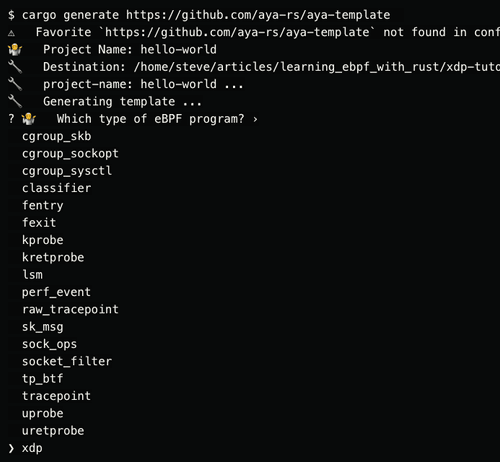
Aya Rust tutorial Part Four XDP Hello World
In the 4th part of the series, learn how to build an XDP program that prints a message every time it receives a packet on an interface
Read more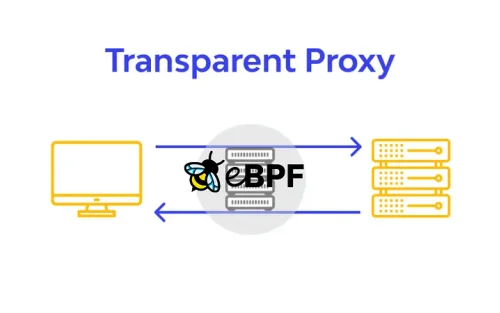
Transparent Proxy Implementation using eBPF and Go
Learn how to implement Transparent proxies with eBPF using the ebpf-go package
Read more
Modernizing BPF for the next 10 years
Explore the future development and modernization of BPF over the next decade, including proposed enhancements, and reflect on its evolution and current capabilities
Read more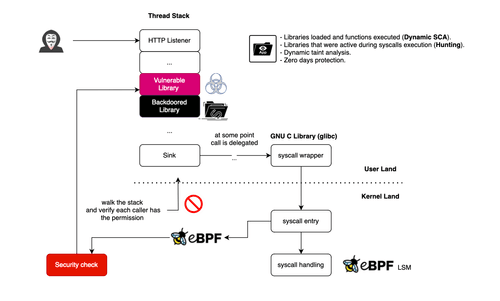
Profiling Libraries With eBPF: Detecting Zero-Day Exploits and Backdoors
Learn how to use eBPF for runtime application security to detect library profile deviations
Read more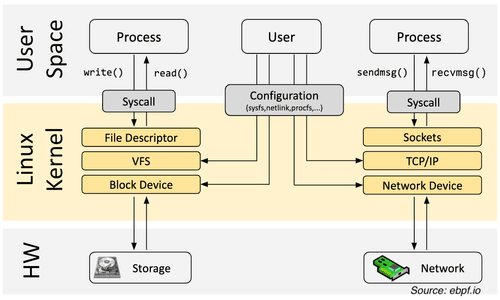
An Applied Introduction to eBPF with Go
Learn what eBPF is, how it works and how to use it with Go
Read more